Limiting or ‘manipulating’ the interests of viewers, readers, listeners, and skewing thoughts and ideals using bad business mentality, where there is a price for attention, pretty pictures, and likeability. Why should you or I be paid to read my book or listen to me speak? Education is not free; we are not in elementary school […]
An Integrated Architecture
An Integrated Architecture What is integrated architecture? In brick-and-mortar terms, or simply building architecture, of which I’m not sure integrated architecture truly exists, would be designed with elements that work together, or parts of each, such as Modern, Masonry, Victorian, Italian, Asian, often associated and varied by culture or timeframe in which it was designed. […]
Law and Compliance Review
Background To establish methods for reviewing and testing compliance, one must understand the structure of the law, its application, its limitations, and how technology is related to the law’s implementation. If no system of compliance exists, then is it even necessary to create rules and compliance if law, regulation, and policy are not a part […]
Policy and Regulation
Listen to associated Podcast: Law, Policy, and Compliance: RDT&E and Standardization What is it, where do I find information on ‘compliance’ and what it means to Information Technology? Is it truly a departmental necessity in every company, or is it built into the research, development, and test phase of the software development lifecycle. What about […]
Identity and Security Design of the Internet
Security Interoperability: A More Efficient Internet Design Research Problem:The Internet does not have a shared data architecture that allows for centralized management of personal information. Each Internet Site that is protected by encryption utilizing a profile and account management system is individualized and users create accounts manually, without an automatic profile copy option. Leveraging account […]
Google’s Sign In With Feature
Why are we okay with massive duplication of our personal information? A mini thesis on risks, benefits, and challenges for users, developers, and companies. There is even some interesting information for investors and security professionals to consider. Profile Security Problems
Software Development Methodologies
Agile, Scrum, DevOps, Lean Development, Waterfall Resources: Software Development Lifecycle Guide – Software Development Life Cycle (SDLC) is a process used by the software industry to design, develop and test high quality softwares. The SDLC aims to produce a high-quality software that meets or exceeds customer expectations, reaches completion within times and cost estimates. These […]
Artificial Intelligence
Artificial Intelligence turned 50 in 2006 (Cordeschi, 2007), making its chronological age 67 in the current year, 2023. The 1956 summer Dartmouth Conference was to examine “the conjecture that every aspect of learning or any other feature of intelligence can in principle be so precisely described that a machine can be made to simulate it,” […]
Improving Focus Area
In review of discussion postings or writing, it is clear there are areas in need of improvement. The most important area to focus on is clarity and succinctness. Clear and concise openings with the research area topic, the problems, the research strategy, how the three topics fit together and quickly present the three articles that relate to the […]
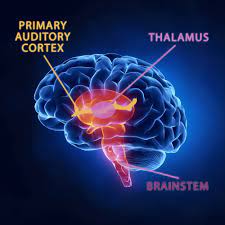
Brain Information Technology
If we had a computer system that could just upload brain changes, remove the negative, unwanted and repetitive thoughts and bad behaviors, we could completely change all of humanity. We don’t – we are humans who have a basic brain, mind, and body living in an environment that is not always healthy. To achieve something, […]
Three Topics in Information Technology
The first IT area has become a rather repetitive non-automated validation process for all systems, where it seems very little information is shared amongst all of the many software applications that use personal data. This is seems to go completely against the purpose of IT, which is streamlined information sharing. It also seems we are […]
Technology and Law Questions of the Week
Was photographic editing available in law enforcement, healthcare, business, and home computer systems in the early 1980s thru the mid 1990s? Research Justification:A child suffered a major injury, causing temporary blindness and potential brain damage. Photographs were available showing pre and post healthcare services which showed significant amount of blood and vision impairment with the […]